END OF LIFE: On 30 April 2014, Sophos unmanaged anti-virus for Unix was terminated. Next version of avfilter will use ClamAV.
Avfilter is a global filter for the Courier-MTA mail system. It scans for viruses using the Sophos anti virus library, a commercial tool.
Avfilter requires a courier and libsavi to be installed (versions < 2.5 required courier sources). A script for email driven virus updates is provided, but not installed.
Note: another approach to anti-virus e-mail filtering provides for installing a separate SMTP server that forwards upon filtering. However, this defeats an SMTP server's ability to discard unwanted mail before committing bandwidth and disk space in some cases.
Starting with version 2, avfilter features a GNU configure script to ease installing. See install.
The filter is loaded by courierfilter. Upon loading, avfilter reads its run-time configuration files, initialises the anti-virus interface, and asks it to load the virus database. See upgrading Sophos software and virus database.
When avfilter is enabled, it is called right after the body of any message has been received but before it is accepted. The main process listens for requests, and forks each time a scan is required. It rewrites each mail message once, undoing any MIME encoding. It scans each attachment by mmapping selected portions of the temporary file and passing them to SAVI (Sophos Anti Virus Interface). The CSAVI3 interface is used with this version. When a virus is detected, the default action is to drop it, that is to mark all recipients as delivered so that no further deliveries or notifications are attempted.
avfilter (and tavfilter)--help--version-f config-file--configverbose is not 0, this will include the options resulting on SAVI.-t file...--batch-testWhen called without parameters avfilter attempts to install itself as a filter. If you do it by accident you may terminate it by closing its standard input or sending a QUIT signal. It will have messed up sockets and pid file, so you are better off stopping and restarting courierfilter. Starting with courier version 0.46, unless configured otherwise, avfilter may avoid the above false-install by checking the file descriptor 3 (fd3-check) from courierfilter.
As a filter, avfilter is called for each message as described above. The process is very simple as only a few points vary:
scan_malformed value:
info to syslog)
action = bounce in the configuration file.
When avfilter receives a reload signal (see avfilter_sig below), it tries to open an output fifo using an hard-coded path. If it succeeds, it uses that instead of stderr during the reload operation.
tavfilter is the debug built of avfilter. Minor differences include not writing a pid file, the output pipe filename defined in the current directory, and a little more verbosity.
avfilter_sigavfilter_sig signals avfilter to reload virus and/or configuration data
syntax:
avfilter_sig --help | --version
or
avfilter_sig [-p pid] [reload [config | virus]]
The --help switch is useful as it displays the full path names of three related files: config, pid and pipe.
In the second form, avfilter_sig sends a signal to avfilter so that the latter reloads its configuration file, the virus data base, or both.
The process id of avfilter can be overridden for testing with -p, otherwise it is read from the pid file.
A named pipe, a.k.a fifo file, is used to read the response. Existence of the pipe is tested to avoid concurrent requests. When the -p option is used avfilter_sig uses ./avfilter_sig.pipe as the pipe name (which works with tavfilter.) For regular operations, avfilter_sig uses the configured pipe name. It expects avfilter to be running with courier privileges and tries to create the pipe with minimal permissions changing its group owner to courier.
The signal sent is
HUP -if neither conf nor virus is specified,
USR1 -for conf, to reload configuration,
USR2 -for virus, to reload the virus data base.
Exit status is 0 if ok, 1 for daemon error, higher for other errors including daemon not running, pipe already in use, etc.
run_get_idesrun_get_ides is a simple xfilter command.
To let it run suid, it loads a fixed shell script. Run run_get_ides -h to check the exact path of the script that will be loaded, as written on the paragraph "The second format is used for invoking ..."
Syntax:
run_get_ides [-D uid/gid] [-t timeout] [--] ...
This xfilter reads both stdout and stderr. The output goes to the
body of the message, as usual. The error is logged on the mail syslog,
except for lines beginning with subject:; in that case
the rest of the line will be the script's "return code", which is
inserted in the message subject, within square brackets. (The last
such line wins.) For syslog errors, the script can decrease the severity
from critical to debug by starting a line with a number of '#
characters.
Recognizing viruses is based on the virus data base currently loaded by SAVI. On disk, it consists of a bulky set of virus data files (vd*) updated on a monthly basis and a number virus identities (*.ide) updated quite frequently. Sophos broadcasts alert messages whenever they updated the monthly version. To use those mails to drive updates, create a dedicated mailbox on your server and xfilter the alerts using run_get_ides to suid to a custom script. Sophos discourages this approach, see here. In my experience, it works perfectly well.
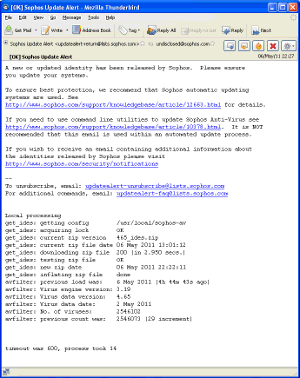
Running get_ides.sh new after installing a new version will do the necessary magic. When run as root, the script changes ownership of the downloaded zip file, and displays on the console the progress that would otherwise be added to the alert message (see left, click to enlarge it.) Xfiltering also modifies the subject, so that when it is [OK] one can skip opening the message.
Monthly updates from Sophos are not advertized. You have to poll their web site (possibly automatically, using curl).
here are the available versions:
| current--> 2.8 | Fri 30 Nov 2012 09:11:41 | [signature] |
| 2.7 | Fri 14 May 2010 14:05:34 | [signature] |
| 2.6 | Sun 28 Feb 2010 19:02:57 | [signature] |
| 2.5 | Mon 25 Aug 2008 08:08:48 | [signature] |
| 2.4 | Tue 19 Dec 2006 13:12:20 | [signature] |
| 2.3 | Sat 18 Nov 2006 08:11:46 | |
| 2.2 | Thu 04 Nov 2004 10:11:13 | |
| 2.1 | Thu 04 Mar 2004 20:03:35 | |
| 2 | Mon 01 Mar 2004 19:03:58 |
I don't think a good anti-virus scanner will ever come for free, because it implies constantly working on the virus data base. This does not mean an anti-virus cannot be open source, but I know about none.
Sophos allows you to download evaluation software. It features a SAVI interface that allows the scanner to be dynamically linked with the application. That betters performance because the anti-virus database is loaded only at startup and because there are no scripts to interpret. SAVI is designed around the Windows COM interface, but is truely multiplatform, as one can run it also on Macs. In addition, the scanner knows how to unpack archives such as zip, gzip, tar, arj, uue, cmz, etc.
I recently (Jan 2006) talked with a representative of Sophos Italia who explained me their special licensing policies for ISPs. If you have some hundred mailboxes or more, then ask to the relevant Sophos branch for details. Otherwise, Sophos charges a few dollars per year per mailbox, which may be totally unsuitable if you have a large user base.
Most computer users today run their own anti-virus product on their client machines. How do they choose one? As an ISP, the only reason I would recommend Sophos to my customers is if that would simplify getting the updates. Commercially, I don't have the ability to earn commissions selling antivirus software to end users, as it's not my business.
Finally, let me state that my commercial relationship with Sophos Italia has nothing to do with this software. I acquired a licence for the few mailboxes I'm running from Studio Gerolimi, an Italian Sophos partner. I obtained the development kit for free from Sophos integration resources.
All the software in the distribution comes under GNU General Public Licence, except for the sophos subdirectory. Sophos headers are copyright of Sophos Plc. They are included in the distribution because they are necessary for compiling avfilter.
If you want to make any derivative work that uses contents of the sophos subdirectory, you cannot grab it from this distribution. You should contact Sophos integration resources. Richard Baldry, product manager for SAV Interface at Sophos, said "It is certainly not our intention to prevent parts of the DTK being included in source trees for open-source type packages. We do not intend for every person who wants to use such a package to have to download the DTK independently."
Julian Mehnle's Courier-Filter is a flexible Perl module. It includes sub-modules for ClamAVd, SPF, DNS black-list, and more.
Gordon Messmer's courier-pythonfilter is a flexible Python module. Some sub-modules are included for specific filtering tasks. Interesting Courier patches may be found in its parent directory.
AMAVIS is a set of scripts for automating e-mail filtering. Utilities for exctracting files from archives are also provided, taking advantage of installed software. A commercial scanner is required.
EPS (Email Processing System) is a set of C-written API for parsing email messages.
the Anomy mail tools featuring Anomy Sanitizer.
I'm currently using this filter and it works quite well. However, I have a specific Courier configuration and version, hence I cannot guarantee that it works smoothly with different settings.
Have fun!